Covid passport: Ticket to normalcy or privacy nightmare

The key features that are suggested to be checked if you are thinking about using a digital vaccination passport app
Hotels: Cyber attackers never sleep

Lately, many cyber attacks disabled hotels around the Europe – hotels in Italy – Valtellina region, UK – Edinburgh and the list goes on and on.
10 Data Backup Mistakes You Can Easily Avoid
Plenty of things can cause data loss. The most common are hardware failure and human error, but software corruption, computer viruses, theft, and natural disasters like floods and fires might occur, as well.
5 Ways to Stop Ransomware

No organization is safe. From hospitals dealing with surges in COVID-19 cases to hotels and restaurant in the Italy to UK train stations — the only rule businesses must learn is that it’s not a case of “if” but “when.”
What is a network operations center (NOC)?
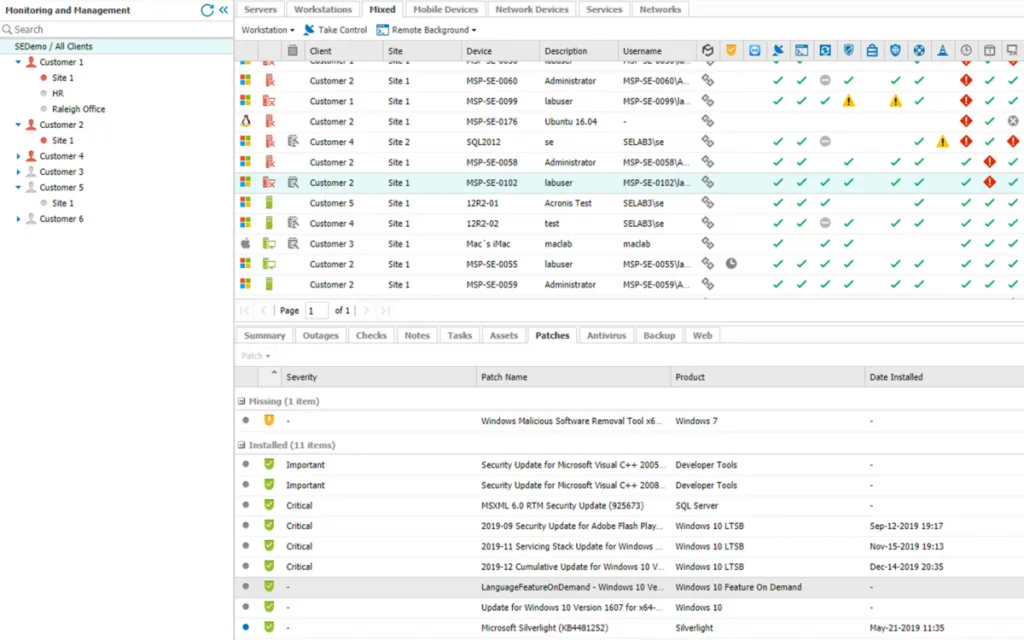
What is a NOC? How does it work? How can network operations center monitoring software help MSPs run their businesses as efficiently as possible? Here’s everything you need to know.
The Future of Remote Work: 8 Ways to Win

Now, many organizations are realizing that there are benefits to having a distributed workforce—if they can solve the biggest technology challenge that remote work presents: network access and management. Remote workers have been wrestling with a plethora of network-related problems, from overly complex login and authentication processes to slow-running apps.
How to watch porn discreetly

We explain who can catch sight of your online activities, and how to make sure your secrets are safe.
Security Specialists vs Developers

Unless you have been under a rock recently, you will have noticed that rarely a day goes by without another serious security problem arising. While there is plenty of blame to go around for these endless security problems, part of this blame is directed towards developers responsible for writing bad code.
What IT security least should your organization meet?

If you’re a small business owner or manager of a bigger company, you’re constantly bombarded with totally different demands or recommendations regarding what your business should or shouldn’t do. Like accounting system, attendance system or whole security system for monitoring cyber threats. However is this really necessary?
What is Ransomware? A few Simple Tips to avoid it

Ransomware is one of the fastest growing cyber security threats in the world but first, let us see exactly what ransomware is?